In Summary
Managed File Transfer (MFT) is an enterprise technology platform that secures, automates, monitors, and governs file transfers across business systems, cloud environments, applications, users, and trading partners.
Unlike traditional FTP or standalone SFTP servers, modern MFT platforms provide:
- centralized governance
- workflow orchestration
- encryption at rest and in transit
- quantum-safe encryption
- audit logging
- compliance controls
- ransomware protection
- operational resiliency
- high availability
- hybrid cloud scalability
Today, MFT has evolved far beyond simple file movement. Modern enterprise MFT platforms now function as critical infrastructure components supporting:
- cybersecurity initiatives
- B2B integration
- EDI operations
- zero trust architectures
- cloud modernization
- operational automation
- enterprise resiliency
Organizations use platforms such as TDXchange to modernize secure data exchange while improving:
- visibility
- governance
- scalability
- automation
- compliance readiness
- business continuity
Key Takeaways
- MFT replaces fragmented file transfer tools with centralized, secure, and automated workflows.
- Modern MFT platforms support enterprise-scale automation, governance, and operational resiliency.
- MFT helps organizations reduce cybersecurity risks associated with unmanaged file sharing and legacy FTP systems.
- Enterprise MFT environments support hybrid cloud, APIs, Kubernetes, and distributed architectures.
- Advanced MFT solutions support clustering, load balancing, failover, and geo-redundancy.
- Modern MFT platforms increasingly support quantum-safe encryption to help future-proof enterprise data security.
- TDXchange helps organizations modernize secure enterprise data exchange while simplifying operational complexity.
What Is Managed File Transfer (MFT)?
Managed File Transfer (MFT) is an enterprise platform used to securely exchange electronic data between:
- enterprise applications
- cloud platforms
- employees
- customers
- suppliers
- APIs
- trading partners
- external systems
MFT platforms centralize:
- file transfer operations
- workflow orchestration
- monitoring
- security enforcement
- compliance auditing
- partner management
Unlike traditional file transfer tools, enterprise MFT solutions provide centralized governance and operational intelligence across distributed environments.
Modern MFT platforms such as TDXchange integrate:
- secure file transfer
- workflow automation
- policy enforcement
- operational visibility
- threat monitoring
- auditability
- scalable infrastructure
into a unified enterprise data exchange platform.
Enterprise Managed File Transfer platforms such as TDXchange help organizations centralize, automate, monitor, and govern secure file transfer operations across hybrid cloud and enterprise environments.
Why Organizations Need Managed File Transfer
Modern organizations exchange enormous amounts of sensitive data every day, including:
- financial transactions
- healthcare records
- EDI transactions
- operational data
- customer information
- payment files
- legal documents
- manufacturing data
- supply chain transactions
Traditional transfer methods often create:
- security vulnerabilities
- operational silos
- visibility gaps
- failed transfers
- compliance risks
- fragmented monitoring
- manual administration
- inconsistent governance
As organizations scale, these limitations become increasingly difficult to manage.
Managed File Transfer addresses these challenges through centralized automation, governance, security, and resiliency.
The Evolution from FTP to Enterprise MFT
Traditional FTP was originally designed for basic file movement — not enterprise security or operational governance.
FTP transfers:
- usernames
- passwords
- file contents
in plaintext, creating major security vulnerabilities.
As cybersecurity threats and compliance requirements evolved, organizations adopted:
- SFTP
- FTPS
- HTTPS
- AS2
- AS4
- enterprise Managed File Transfer platforms
Modern MFT environments evolved to support:
- encryption
- automation
- centralized administration
- policy enforcement
- operational monitoring
- audit logging
- resiliency
- cloud integration
- zero trust security models
This transformed file transfer from a simple utility into a foundational enterprise integration and cybersecurity capability.
How Does MFT Work?
Managed File Transfer platforms centralize and automate secure enterprise data exchange workflows across applications, cloud environments, users, and trading partners.
Typical Enterprise MFT Workflow
1. File Generation
A business application, system, user, or automated process generates a file that needs to be securely exchanged.
Examples include:
- EDI transactions
- purchase orders
- invoices
- payment files
- healthcare records
- analytics exports
- supply chain documents
- batch processing outputs
Files may originate from:
- ERP systems
- databases
- cloud applications
- APIs
- user uploads
- enterprise applications
- IoT devices
- external partner systems
2. File Ingestion into the MFT Platform
The file is then uploaded, transferred, detected, or collected by the MFT platform.
MFT platforms support multiple ingestion methods, including:
- monitored folder pickup
- direct uploads
- API ingestion
- cloud storage synchronization
- agent-based collection
- scheduled polling
- event-driven triggers
- partner-initiated transfers
Files may enter the MFT environment through:
- SFTP
- FTPS
- HTTPS
- AS2
- AS4
- APIs
- web portals
- relay/proxy gateways
Modern enterprise MFT platforms often use DMZ-based relay architectures to securely isolate external traffic from internal systems.
3. Workflow Orchestration
Once ingested, the MFT platform automatically applies:
- routing rules
- workflow logic
- metadata validation
- naming conventions
- transfer schedules
- SLA policies
- automation triggers
Advanced enterprise MFT workflows may also support:
- event-driven processing
- conditional routing
- multi-step workflows
- API-triggered automation
- intelligent retries
- transfer prioritization
- partner-specific policy enforcement
4. Security Enforcement
The MFT platform secures files using:
- encryption in transit
- encryption at rest
- digital signatures
- checksum validation
- malware scanning
- DLP inspection
- quantum-safe encryption
Security policies may also include:
- IP filtering
- denial-of-service protection
- file integrity verification
- certificate validation
- threat intelligence integration
5. Authentication & Authorization
Enterprise MFT platforms validate:
- users
- systems
- APIs
- certificates
- SSH keys
- access permissions
Integration commonly includes:
- LDAP
- Active Directory
- SAML
- OAuth
- MFA
Modern MFT platforms increasingly support identity-aware security policies aligned with Zero Trust security frameworks.
6. Secure File Transfer & Delivery
The MFT platform securely transfers files to:
- trading partners
- cloud platforms
- internal systems
- APIs
- storage platforms
- downstream applications
Protocols commonly include:
- SFTP
- FTPS
- HTTPS
- AS2
- AS4
Clustered relay/proxy architectures and load balancers may distribute traffic across multiple nodes to improve:
- scalability
- throughput
- resiliency
- high availability
7. Monitoring & Operational Visibility
The MFT platform continuously monitors:
- transfer activity
- throughput
- failures
- retries
- SLA compliance
- partner connectivity
- infrastructure health
Centralized dashboards provide real-time operational visibility across distributed enterprise environments.
Advanced monitoring may include:
- anomaly detection
- behavioral analysis
- transfer analytics
- predictive alerting
- infrastructure observability
8. Audit Logging & Compliance Tracking
Detailed logs capture:
- transfer history
- authentication events
- workflow execution
- policy enforcement
- delivery confirmations
- security events
This supports:
- compliance reporting
- forensic investigations
- governance initiatives
- operational auditing
Tamper-resistant audit logging is increasingly critical for regulated industries and cybersecurity frameworks.
9. Automation, Recovery & Failover
Advanced MFT platforms automate:
- retries
- notifications
- workflow escalation
- checkpoint restart
- disaster recovery
- failover handling
- partner onboarding
This improves operational resiliency and reduces manual intervention.
Enterprise-grade MFT environments often support:
- clustering
- geo-redundancy
- active-active deployments
- load balancing
- automated node failover
- transfer checkpoint recovery
What Security Protocols Do MFT Platforms Support?
Modern MFT solutions support multiple secure file transfer and B2B communication protocols that enable encrypted, automated, reliable, and compliant data exchange across enterprise systems, cloud environments, APIs, and trading partner ecosystems.
Different protocols are designed for different:
- transport models
- security requirements
- authentication methods
- workflow architectures
- integration use cases
Enterprise MFT platforms such as TDXchange often support multiple protocols simultaneously to simplify interoperability across complex hybrid enterprise environments.
SFTP (SSH File Transfer Protocol)
SFTP is a secure file transfer protocol that operates over SSH (Secure Shell), typically using TCP port 22.
Unlike traditional FTP, SFTP encrypts:
- authentication credentials
- commands
- file contents
- session traffic
within a secure SSH tunnel.
SFTP supports:
- encrypted communications
- public/private key authentication
- password authentication
- integrity validation
- secure remote administration
- file management operations
A typical SFTP session involves:
- SSH handshake negotiation
- Key exchange algorithm negotiation
- Cipher and hashing selection
- User or key-based authentication
- Encrypted session establishment
- Secure file transfer operations
Common cryptographic algorithms include:
- AES-256
- RSA
- ECDSA
- Ed25519
- SHA-2
SFTP is widely used for:
- server-to-server automation
- enterprise batch processing
- secure partner communications
- internal file exchange
- cloud integrations
Because SFTP combines secure transport and remote file operations within a single protocol, it remains one of the most commonly deployed secure file transfer protocols in enterprise environments.
FTPS (File Transfer Protocol Secure)
FTPS extends traditional FTP by adding SSL/TLS encryption for secure communications.
FTPS supports:
- encrypted control channels
- encrypted data channels
- X.509 certificate authentication
- TLS-based communications
- secure client/server validation
There are two primary FTPS modes:
- Explicit FTPS (recommended modern approach)
- Implicit FTPS (legacy implementation)
FTPS is commonly used in environments requiring:
- compatibility with existing FTP workflows
- encrypted file transfer
- certificate-based authentication
- legacy system modernization
Organizations often deploy FTPS when upgrading older FTP environments without redesigning existing operational processes.
HTTPS (Hypertext Transfer Protocol Secure)
HTTPS secures browser-based and API-driven file transfers using TLS encryption.
HTTPS is commonly used for:
- browser uploads/downloads
- secure web portals
- REST APIs
- cloud integrations
- SaaS applications
- remote workforce access
HTTPS supports:
- TLS encryption
- certificate validation
- identity-aware access controls
- secure API communications
- session integrity
Modern enterprise integration architectures increasingly rely on HTTPS-based APIs and web services for secure application-to-application communication and cloud-native data exchange.
AS2 (Applicability Statement 2)
AS2 is a secure B2B communication protocol widely used for EDI and supply chain integration over the internet.
AS2 securely transmits EDI and business documents using:
- HTTP or HTTPS transport
- S/MIME packaging
- digital certificates
- encryption
- digital signatures
AS2 messages are encapsulated using S/MIME (Secure/Multipurpose Internet Mail Extensions) over HTTP/S, allowing organizations to securely exchange structured business documents directly over the internet without relying on traditional VANs.
AS2 supports:
- payload encryption
- digital signatures
- message integrity verification
- MDN acknowledgments (Message Disposition Notifications)
- non-repudiation
- certificate-based authentication
A typical AS2 workflow includes:
- The sender packages the payload using S/MIME
- The payload is digitally signed
- The message is encrypted using the recipient’s public certificate
- The message is transmitted over HTTP or HTTPS
- The recipient validates the signature and decrypts the payload
- An MDN acknowledgment confirms successful receipt
AS2 commonly uses:
- X.509 certificates
- PKCS#7 signatures
- SHA-256 hashing
- AES encryption
AS2 is heavily used across:
- retail
- manufacturing
- logistics
- healthcare
- supply chain ecosystems
Major retailers and global supply chains frequently require AS2 for EDI communications because it provides:
- secure internet-based B2B exchange
- transaction traceability
- compliance support
- reliable acknowledgments
- strong auditability
AS4 (Applicability Statement 4)
AS4 is a modern B2B messaging protocol designed for secure, scalable, and service-oriented enterprise integration.
AS4 is built on:
- SOAP web services
- ebMS 3.0 (ebXML Messaging Services)
- WS-Security standards
Unlike AS2, which primarily relies on HTTP/S and S/MIME packaging, AS4 uses web services architecture to support more flexible and scalable enterprise integration models.
AS4 supports:
- secure SOAP messaging
- reliable messaging
- payload compression
- asynchronous communication
- message persistence
- advanced security frameworks
- cloud-native integration architectures
- multi-hop routing
- large payload handling
AS4 security capabilities include:
- XML digital signatures
- message-level encryption
- certificate-based authentication
- integrity validation
- non-repudiation
AS4 messages are typically exchanged using:
- SOAP envelopes
- XML payload structures
- WS-Security headers
- ebMS messaging frameworks
A typical AS4 workflow includes:
- Business payload creation
- SOAP message encapsulation
- WS-Security signature application
- Message encryption
- Reliable messaging configuration
- HTTPS transmission
- Receipt acknowledgment and validation
AS4 is particularly valuable for:
- modern API-driven ecosystems
- international B2B communications
- hybrid cloud environments
- distributed enterprise architectures
- large-scale partner ecosystems
AS4 improves interoperability while supporting:
- service-oriented architectures (SOA)
- microservices integration
- cloud-native deployments
- modern enterprise integration platforms
AS4 adoption continues increasing across:
- government networks
- healthcare
- logistics
- global supply chains
- European B2B integration ecosystems
Many organizations view AS4 as the evolution of AS2 for modern distributed enterprise integration architectures.
APIs (Application Programming Interfaces)
Modern MFT platforms increasingly support API-based file transfer and workflow integration.
APIs enable:
- real-time integrations
- event-driven automation
- application-to-application communication
- cloud-native orchestration
- DevOps workflows
RESTful APIs commonly use:
- HTTPS transport
- OAuth authentication
- JWT tokens
- TLS encryption
- JSON or XML payloads
API-driven MFT architectures are commonly used for:
- cloud platforms
- SaaS integrations
- microservices
- enterprise automation
- modern application ecosystems
Modern MFT platforms frequently expose APIs for:
- transfer initiation
- workflow orchestration
- partner onboarding
- monitoring
- audit retrieval
- administrative automation
WebDAV (Web Distributed Authoring and Versioning)
WebDAV extends HTTP/HTTPS to support collaborative file management and remote content authoring.
WebDAV supports:
- remote file editing
- document collaboration
- centralized repositories
- secure web-based access
- distributed content management
WebDAV is commonly used for:
- remote workforce collaboration
- distributed file access
- browser-based file management
- centralized document repositories
PeSIT
PeSIT is a secure file transfer protocol commonly used in European banking, financial services, and regulated enterprise environments.
PeSIT supports:
- reliable file delivery
- transfer checkpointing
- restart/recovery handling
- transaction integrity
- secure enterprise communications
PeSIT is heavily used for:
- banking transactions
- financial reporting
- regulated B2B communications
- large enterprise data exchange
OFTP2 (Odette File Transfer Protocol 2)
OFTP2 is a secure file transfer protocol widely used in automotive and manufacturing supply chains.
OFTP2 supports:
- encryption
- digital certificates
- payload compression
- restart/recovery capabilities
- large file transfer optimization
- secure B2B communications
OFTP2 is commonly used across:
- automotive ecosystems
- manufacturing supply chains
- global partner networks
- international B2B environments
Its checkpoint restart capabilities make it highly efficient for transferring large engineering and manufacturing files.
Supporting multiple protocols allows enterprise MFT platforms such as TDXchange to securely exchange data across:
- cloud platforms
- hybrid environments
- APIs
- ERP systems
- trading partners
- distributed enterprise architectures
while maintaining:
- security
- interoperability
- operational resiliency
- compliance
- scalability
- future-ready enterprise integration capabilities.
Why Quantum-Safe Encryption Matters for Modern MFT
Quantum computing is expected to fundamentally reshape modern cybersecurity and encryption strategies.
Traditional cryptographic algorithms such as:
- RSA
- ECC
- Diffie-Hellman
could eventually become vulnerable to sufficiently powerful quantum computers capable of breaking conventional public key encryption.
For organizations exchanging sensitive long-lived data such as:
- healthcare records
- financial transactions
- government communications
- intellectual property
- legal documents
- critical infrastructure data
this creates significant long-term cybersecurity concerns.
What Is Quantum-Safe Encryption?
Quantum-safe encryption, also known as post-quantum cryptography (PQC), refers to cryptographic algorithms specifically designed to resist attacks from both:
- classical computers
- future quantum computers
These technologies are actively being standardized by organizations such as:
Why Quantum-Safe Security Matters for MFT
Threat actors increasingly use:
“harvest now, decrypt later”
strategies where encrypted data is stolen today with the expectation that future quantum computers may eventually decrypt it.
Managed File Transfer platforms often store and transfer highly sensitive information that may remain valuable for years or decades.
This makes long-term cryptographic protection increasingly important for:
- healthcare
- finance
- government
- defense
- critical infrastructure
- supply chain ecosystems
Quantum-Safe Encryption in TDXchange
bTrade was among the first enterprise MFT vendors to introduce quantum-safe encryption capabilities into modern Managed File Transfer environments.
TDXchange helps organizations future-proof secure data exchange through:
- quantum-safe cryptographic support
- encryption modernization
- secure key management
- advanced data protection
- long-term compliance readiness
This helps organizations strengthen both current and future cybersecurity posture as quantum computing technologies continue evolving.
Enterprise-Grade MFT Architecture
Modern MFT platforms increasingly support enterprise-scale distributed architectures.
High Availability Clustering
Enterprise MFT clustering enables:
- workload distribution
- failover protection
- transfer continuity
- resiliency
- scalability
Clustered environments prevent single points of failure.
Load Balancing
Load balancers distribute transfer traffic across:
- multiple relay nodes
- clustered servers
- geographically distributed environments
This improves:
- performance
- throughput
- scalability
- resiliency
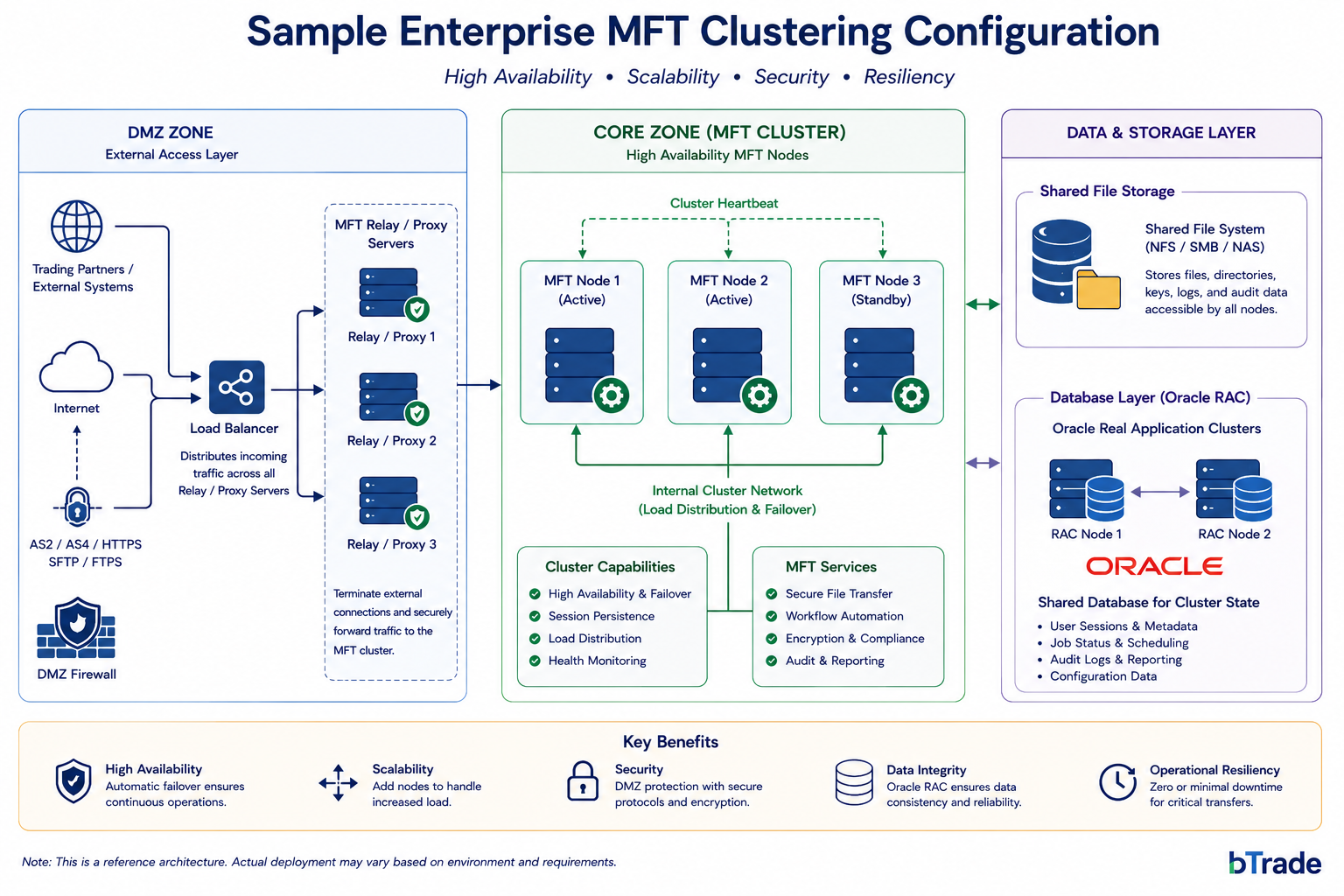
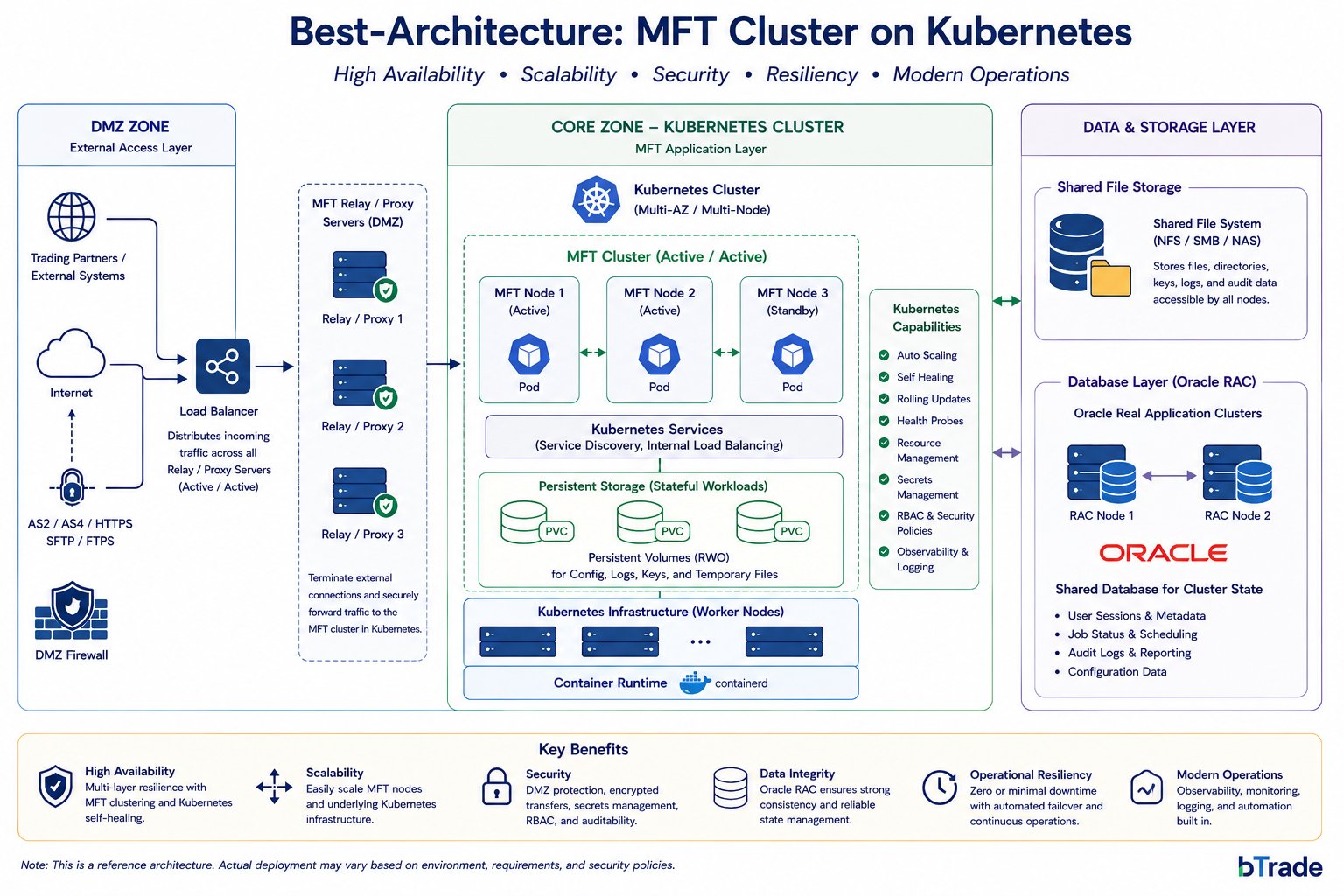
Kubernetes & Containerization
Modern MFT platforms increasingly support:
- Kubernetes orchestration
- containerized deployments
- cloud-native scalability
- hybrid cloud architectures
However, enterprise file transfer workloads are highly stateful and require careful architectural planning involving:
- persistent storage
- synchronized metadata
- transfer checkpointing
- session continuity
- transactional integrity
According to the official Kubernetes documentation, Kubernetes automates deployment, scaling, and management of containerized applications.
Organizations implementing stateful MFT workloads within Kubernetes environments often leverage:
- Kubernetes StatefulSets
- distributed storage
- persistent volumes
- clustered databases
to maintain enterprise-grade resiliency.
Geo-Redundancy
Geo-redundant deployments improve:
- disaster recovery
- business continuity
- regional resiliency
- uptime guarantees
This is especially important for:
- financial services
- healthcare
- government
- critical infrastructure
Core Features of Enterprise MFT Software
Centralized Governance
MFT platforms centralize:
- users
- workflows
- transfers
- policies
- partner management
- reporting
Platforms like TDXchange eliminate fragmented transfer environments and improve operational control.
Workflow Automation
Enterprise MFT automation supports:
- event-driven processing
- scheduled transfers
- intelligent routing
- retry logic
- SLA enforcement
- workflow orchestration
Automation reduces:
- manual effort
- operational delays
- human error
- failed transfers
Advanced Security Controls
Modern MFT security capabilities include:
- encryption at rest
- encryption in transit
- quantum-safe encryption
- MFA
- RBAC
- IP filtering
- malware scanning
- threat monitoring
- anomaly detection
- DLP integration
Modern MFT increasingly aligns with:
- Zero Trust architectures
- NIST Cybersecurity Framework
- enterprise cybersecurity standards
Audit Logging & Compliance
MFT platforms generate detailed audit trails for:
- transfers
- user activity
- authentication events
- policy changes
- workflow execution
These capabilities support:
- HIPAA
- GDPR
- PCI DSS
- SOX
- NIST
- internal governance policies
Tamper-resistant logging improves:
- compliance reporting
- forensic analysis
- operational accountability
Why MFT Matters for Cybersecurity
File transfer environments are increasingly targeted by:
- ransomware
- credential theft
- phishing attacks
- supply chain attacks
- insider threats
- data exfiltration
MFT reduces these risks through:
- centralized governance
- encrypted communications
- secure authentication
- policy enforcement
- operational visibility
- anomaly detection
- auditability
Modern MFT transforms file transfer from a security liability into a governed enterprise service.
MFT and Zero Trust Security
Modern enterprises increasingly align MFT environments with Zero Trust principles.
Zero Trust assumes:
no user, device, or workload is inherently trusted.
MFT supports Zero Trust through:
- continuous authentication
- least-privilege access
- segmented workflows
- encrypted communications
- identity-aware policies
- behavioral monitoring
This significantly improves enterprise cybersecurity posture.
How MFT Supports Compliance Requirements
Organizations handling sensitive data often face strict regulatory requirements.
MFT platforms help organizations support:
- HIPAA
- GDPR
- PCI DSS
- SOX
- NIST
- internal governance policies
Key compliance capabilities include:
- detailed audit logging
- encryption at rest
- transfer monitoring
- role-based permissions
- centralized reporting
- tamper-resistant logs
These controls improve audit readiness and reduce compliance risk.
What Industries Use Managed File Transfer?
Managed File Transfer is widely used across industries that require secure, compliant, and reliable data exchange.
Healthcare
Healthcare organizations use MFT for:
- patient records
- claims processing
- HIPAA compliance
- secure provider communications
Financial Services
Banks and financial institutions use MFT for:
- transaction processing
- payment files
- fraud prevention
- auditability
- secure customer data exchange
Manufacturing
Manufacturers use MFT for:
- supply chain automation
- EDI transactions
- operational workflows
- partner coordination
Retail
Retail organizations use MFT for:
- inventory synchronization
- supplier onboarding
- shipment notifications
- order processing
Government and Critical Infrastructure
Government agencies and infrastructure providers use MFT for:
- secure communications
- policy enforcement
- operational resiliency
- centralized governance
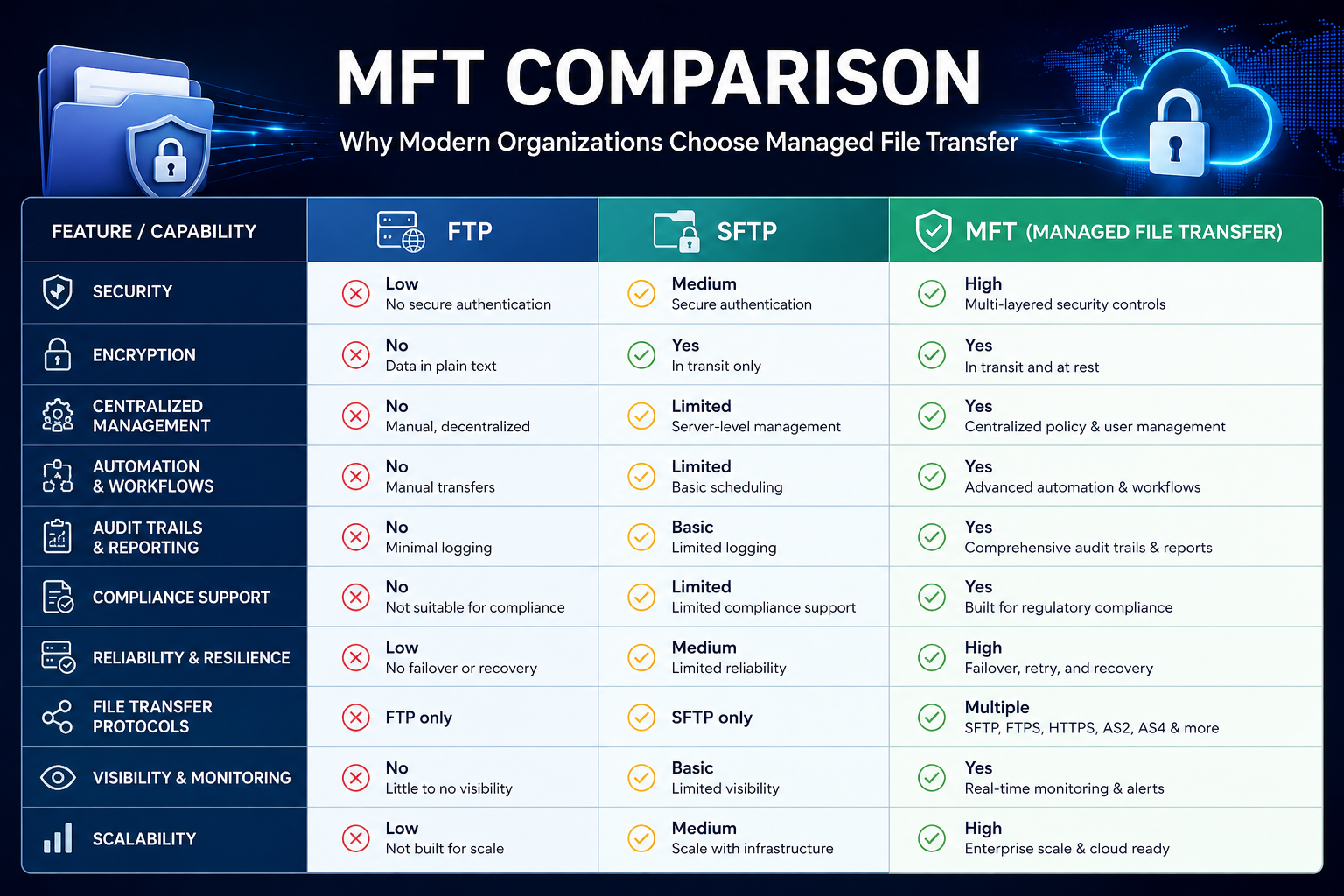
MFT vs FTP: What Is the Difference?
FTP
Traditional FTP:
- transfers data in plaintext
- lacks encryption
- provides limited security
- offers minimal visibility
- does not support compliance requirements
MFT
Managed File Transfer provides:
- encrypted transfers
- centralized governance
- automation
- audit logging
- compliance controls
- operational monitoring
- workflow orchestration
MFT is designed for modern enterprise security and scalability requirements.
MFT vs SFTP
SFTP secures file transfers using SSH encryption but primarily focuses on transport security.
Managed File Transfer platforms build on protocols like SFTP while adding:
- centralized administration
- automation
- compliance controls
- resiliency
- monitoring
- governance
- ransomware protection
Organizations with growing operational complexity often move from standalone SFTP environments to enterprise MFT platforms such as TDXchange.
How MFT Supports Modern Enterprise Architecture
Modern enterprises operate across:
- hybrid cloud environments
- APIs
- remote workforces
- partner ecosystems
- cloud storage platforms
- ERP systems
- distributed applications
MFT platforms support these environments through:
- centralized orchestration
- secure automation
- scalable integrations
- operational visibility
- resilient transfer workflows
MFT increasingly plays a foundational role in enterprise integration and digital transformation strategies.
Best Practices for Implementing MFT
Define File Transfer Requirements
Organizations should identify:
- transfer volumes
- security requirements
- compliance obligations
- partner integrations
- workflow complexity
- scalability needs
Implement Strong Access Controls
Best practices include:
- multi-factor authentication
- least-privilege access
- SSH key management
- role-based permissions
- centralized identity integration
Automate Workflows
Automation reduces:
- manual effort
- operational delays
- transfer failures
- security gaps
Monitor File Transfer Activity
Continuous monitoring improves:
- visibility
- incident response
- compliance reporting
- operational awareness
Support High Availability
Enterprise MFT environments should include:
- clustering
- failover
- disaster recovery
- load balancing
- resilient architecture
Why Organizations Choose TDXchange
Organizations choose TDXchange because it helps modernize enterprise file transfer while improving:
- security
- governance
- scalability
- resiliency
- compliance
- automation
- operational visibility
- hybrid cloud readiness
TDXchange supports:
- clustering
- Kubernetes
- high-volume transfer environments
- secure B2B integration
- centralized governance
- enterprise-scale automation
- quantum-safe encryption
A Proven Pioneer in Managed File Transfer
bTrade has been one of the pioneers in the Managed File Transfer industry for decades.
The company’s first enterprise file transfer solutions were originally developed in the early 1990s, long before modern MFT became a mainstream enterprise category. From the beginning, bTrade focused on solving large-scale enterprise data exchange, security, and operational reliability challenges for highly regulated industries and complex B2B ecosystems.
Over the years, bTrade has continuously evolved its technology to address emerging enterprise integration and cybersecurity requirements.
Key innovations include:
- early enterprise-grade secure file transfer automation
- high-volume EDI and B2B integration support
- accelerated file transfer technologies introduced in the early 2000s
- advanced clustering and high-availability architectures
- hybrid cloud and Kubernetes-ready deployments
- Zero Trust security alignment
- quantum-safe encryption capabilities
This long history gives bTrade deep operational experience in designing enterprise-grade secure data exchange architectures that scale reliably over time.
Accelerated File Transfer Innovation
As enterprise data volumes rapidly increased in the early 2000s, bTrade introduced Accelerated File Transfer capabilities designed to optimize:
- large file movement
- high-latency network performance
- global data exchange
- WAN optimization
- transfer reliability
Accelerated transfer technologies became increasingly important for organizations handling:
- global supply chain operations
- media files
- healthcare imaging
- financial transaction data
- large enterprise workloads
Today, modern enterprise environments continue requiring high-performance transfer architectures capable of supporting globally distributed operations and massive data growth.
Early Adoption of Quantum-Safe Encryption & Zero Trust
bTrade was also among the first enterprise MFT vendors to introduce:
- quantum-safe encryption
- Zero Trust security principles
- advanced identity-aware security controls
into modern MFT environments.
As quantum computing and modern cyber threats continue evolving, organizations increasingly need long-term encryption strategies capable of protecting sensitive data against both:
- current threats
- future cryptographic risks
TDXchange helps organizations future-proof secure data exchange through:
- post-quantum cryptography support
- advanced encryption modernization
- identity-aware access controls
- centralized governance
- Zero Trust-aligned architecture
- operational visibility
- enterprise-grade auditability
This enables organizations to strengthen both immediate and long-term cybersecurity posture.
Recognized Industry Leadership
bTrade and TDXchange have consistently been recognized for customer satisfaction, enterprise capabilities, and operational reliability.
TDXchange has ranked as the #1 Managed File Transfer solution by Software Reviews for the last four consecutive years, reflecting strong customer feedback around:
- product capabilities
- operational reliability
- vendor support
- architecture flexibility
- enterprise scalability
- customer partnership
This recognition reinforces bTrade’s long-standing reputation as a trusted enterprise MFT provider.
Architecture-First Approach to Customer Success
At bTrade, we understand that long-term success in enterprise Managed File Transfer environments depends heavily on getting the architecture right from the beginning.
Many organizations struggle with:
- operational complexity
- scaling limitations
- fragmented automation
- resiliency gaps
- visibility challenges
not because of the platform itself, but because the original architecture was not designed for long-term growth and operational demands.
That is why bTrade spends significant time working closely with customers to design architectures aligned with:
- operational requirements
- security objectives
- scalability goals
- compliance mandates
- hybrid cloud strategies
- disaster recovery planning
- future modernization initiatives
This architecture-first approach helps organizations build MFT environments that remain:
- scalable
- resilient
- secure
- maintainable
- future-ready
as enterprise ecosystems continue evolving.
Long-Term Enterprise Partnership
bTrade’s approach goes beyond simply delivering software.
The company works closely with customers as a long-term technology partner focused on:
- operational success
- architectural guidance
- modernization strategies
- cybersecurity evolution
- integration scalability
- continuous optimization
This collaborative model helps organizations confidently modernize secure enterprise data exchange while reducing long-term operational risk and complexity.
Common Enterprise MFT Platforms
Organizations evaluating Managed File Transfer platforms often compare:
- TDXchange
- MOVEit
- GoAnywhere MFT
- IBM Sterling
- Axway
- Cleo
- Kiteworks
Final Thoughts
Managed File Transfer has become a critical enterprise technology for organizations that need secure, automated, compliant, and scalable data exchange.
As cybersecurity threats, compliance pressures, and operational complexity continue increasing, businesses are moving beyond fragmented transfer tools and standalone FTP or SFTP servers toward centralized MFT platforms.
Modern MFT solutions such as TDXchange help organizations improve:
- security
- automation
- governance
- auditability
- resiliency
- operational efficiency
- business continuity
MFT is no longer just about moving files securely. It is now a foundational component of modern enterprise integration, cybersecurity, and digital transformation strategies.
About the Author
Andrei Olin is Chief Technology Officer at bTrade, where he leads product strategy, delivery, and security across the company’s B2B, Managed File Transfer (MFT), and security platforms. He brings over 30 years of experience in enterprise technology, including designing and operating mission-critical MFT and messaging platforms for global financial institutions such as Merrill Lynch and Deutsche Bank. Andrei holds Master’s and Bachelor’s degrees in Information Technology with a focus on Information Security.
FAQs
What is Managed File Transfer (MFT)?
Managed File Transfer (MFT) is an enterprise platform that secures, automates, monitors, and governs file transfers across systems, users, cloud platforms, and trading partners.
How is MFT different from FTP?
FTP transfers data in plaintext and lacks enterprise security controls. MFT provides encryption, automation, centralized governance, audit logging, monitoring, and compliance support.
Does MFT provide better security than standalone SFTP?
Yes. While SFTP encrypts data during transmission, MFT platforms add:
- encryption at rest
- workflow automation
- audit logging
- centralized visibility
- compliance reporting
- operational resiliency
What compliance regulations does MFT support?
MFT platforms commonly help organizations support:
- HIPAA
- GDPR
- PCI DSS
- SOX
- NIST
- internal governance policies
What industries use Managed File Transfer?
Industries commonly using MFT include:
- healthcare
- finance
- manufacturing
- retail
- logistics
- government
- critical infrastructure
What protocols do MFT platforms support?
Modern MFT platforms support:
- SFTP
- FTPS
- HTTPS
- AS2
- AS4
- APIs
- hybrid cloud integrations
Why do enterprises use MFT?
Organizations use MFT to improve:
- cybersecurity
- compliance
- automation
- operational visibility
- scalability
- auditability
- business continuity
Can MFT support hybrid cloud environments?
Yes. Modern MFT platforms support:
- hybrid cloud
- Kubernetes
- cloud storage
- APIs
- distributed enterprise architectures
Why are organizations moving away from FTP?
Organizations are replacing FTP because it lacks:
- encryption
- compliance controls
- centralized governance
- audit logging
- operational resiliency
- modern cybersecurity protections
What is TDXchange?
TDXchange is bTrade’s enterprise Managed File Transfer platform designed to help organizations secure, automate, monitor, and govern enterprise data exchange and file transfer operations.

